Mobile apps have become the primary engagement channel for modern businesses. Whether it’s a healthcare portal, an e-commerce platform, a retail app, or a telecom service, customers are logging in, transacting, and relying on these apps every day. But with that convenience comes risk. As mobile apps grow more powerful, they’re also becoming prime targets for cyberattacks and the consequences of a breach are only becoming more severe.
In 2024, the average cost of a breach in the retail industry rose to $3.48 million, up from $2.96 million in 2023. Healthcare organizations saw even steeper losses, with breach costs averaging $9.77 million per incident. The E-commerce and technology sectors also experienced surging breach costs, often tied to overlooked mobile vulnerabilities. These aren’t just abstract numbers they reflect real fallout: revenue loss, customer churn, compliance penalties, and lasting brand damage.
Cyberattacks on mobile platforms have already triggered multi-million-dollar losses across industries. In retail and e-commerce, breaches during peak seasons have caused widespread service disruptions, financial damage, and reputational fallout. In healthcare, several major breaches in 2024 compromised the personal data of over 190 million people, with total response and recovery costs projected to exceed $1.6 billion. These incidents drive home a hard truth: a single breach can derail a business regardless of industry.
Telecom providers have also faced growing mobile security threats. In one case, exposed APIs and internal tools led to SIM-swap attacks that caused over $220 million in damages and legal fallout. These cases highlight the risks telecom apps face and the need for multi-layer protection and auditability.
Reputational and operational losses often exceed direct financial losses. Beyond legal costs, companies must contend with lost customer trust, brand erosion, and internal disruption. Recovery isn’t measured in days—but in quarters. Rebuilding confidence, satisfying regulators, and fixing broken processes can take far longer than containing the breach itself. That’s why speed, transparency, and proactive defense are now business-critical—not just IT concerns.
The rising breach costs across industries speak for themselves:
So how do you stay ahead? It starts with shifting from a reactive approach to proactive, instant defense. According to IBM’s 2024 Cost of a Data Breach Report:
- Organizations that implemented AI and automation saved an average of $2.22 million per breach
- They also contained incidents 108 days faster than those without automated capabilities
While AI is still evolving in mobile security, the takeaway is clear: speed and automation matter. That’s where V-OS App Shield delivers immediate value today. It provides real-time, code-free protection that can be deployed in minutes enabling faster response, shorter exposure windows, and stronger mobile security posture across industries.
V-OS App Shield delivers exactly that. Built for businesses that need security at scale without slowing down, it’s a cloud-based, no-code mobile app protection solution that wraps your app with enterprise-grade defenses in minutes—no code changes required.
V-OS App Shield provides:
- Root and emulator detection to block execution in compromised or simulated environments
- Malware detection to identify and block malicious software injected into the app from infecting mobile devices and apps
- Anti-tampering and runtime integrity checks to prevent code modification and unauthorized changes
- Secure data binding to tie sensitive app data to a specific, trusted device
- Real-time threat protection against malware injection, dynamic hooking, and other runtime attacks
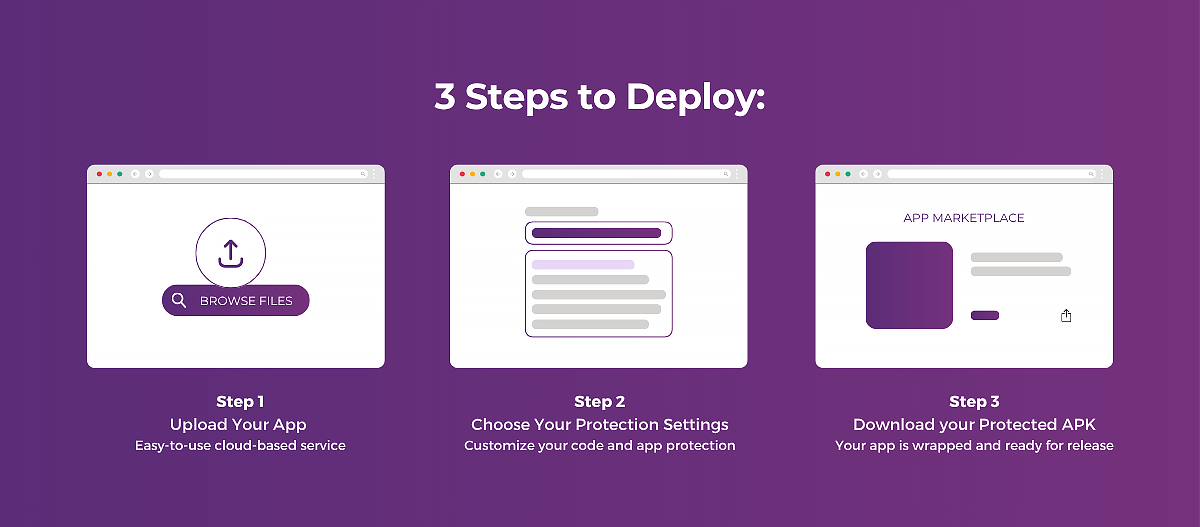
Because it’s easy to integrate and deploy in minutes, V-OS App Shield is ideal for teams that prioritize speed and efficiency without compromising security in industries like E-commerce, Healthcare, Logistics, Telecommunication and more, especially those operating in high-pressure cycles or rapid release environments.
Mobile breaches are hitting every industry, and they’re getting more expensive. But with V-OS App Shield, the right defense is already here. Proactive, instant protection isn’t just better security; it’s better business.
If you’re responsible for securing your organization’s mobile app, now is the time to take action. Contact us today.
Reference: Chamber Store Age, Chief Healthcare Executive, IBM cost of a data breach report, Reute